Windows XP user? One security threat and counting
A new Internet Explorer zero-day vulnerability is currently being exploited in the wild. The vulnerability, identified this week, affects all versions of Internet Explorer including the archaic versions 6 through 8 which ship with the now-dead Windows XP.
This newly discovered flaw, also known as CVE-2014-1776, leverages a Flash exploitation technique that loads an SWF file to corrupt process memory and direct the program’s flow to a memory location where malicious code is laid out. This exploitation technique can bypass the two most important security mechanisms in Windows: DEP (Data Execution Prevention) and ASLR (Address Space Layout Randomisation).
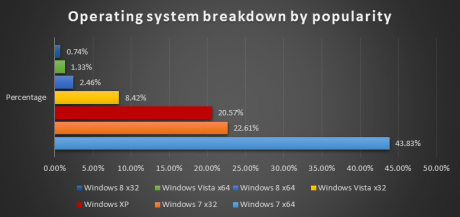
While a zero-day attack against an application as popular as Internet Explorer is serious business, things are even worse for a special category: the Windows XP users. Less than three weeks ago, Microsoft shipped the last security update for 20-something per cent of Windows users with the firm promise that it would be the last one ever.
Windows OS breakdown by popularity. Source: Bitdefender Labs data
Another significant issue is the fact that Windows is closely tied to Internet Explorer -- it is an important component of the operating system that is hardcoded in every edition of the OS, even after the installation of the EU-friendly Browser Choice update.
Last but not least, many still think that computer users running Windows XP are using anything but Internet Explorer on their set-ups. While this may be true for regular users, the situation in enterprise environments is exactly the opposite. Actually, this is one of the reasons companies have lagged behind for so long with the upgrade process: the incompatibility of their custom applications with Internet Explorer versions 7 and up. Which is why, 12 years later, Windows XP is still world’s second most popular operating system. And, if you’re thinking about the cost of migration, now you should be thinking about the cost of not migrating.
Now strap yourself for the really bad news. Whenever a zero-day exploit against the browser is discovered, it is just a matter of days until it becomes public knowledge (read: it is pushed in an exploit pack or in a penetration testing framework such as Metasploit), making payload generation a breeze even for the unexperienced. This means that in just a couple of days we’re going to see all (or at least the most important) exploit packs updated to automatically throw freshly baked malicious code at completely unprotected users. And, while this will soon be over for users of supported versions of Windows (as Microsoft is readying a fix), XP users will remain vulnerable forever.
What to do now?
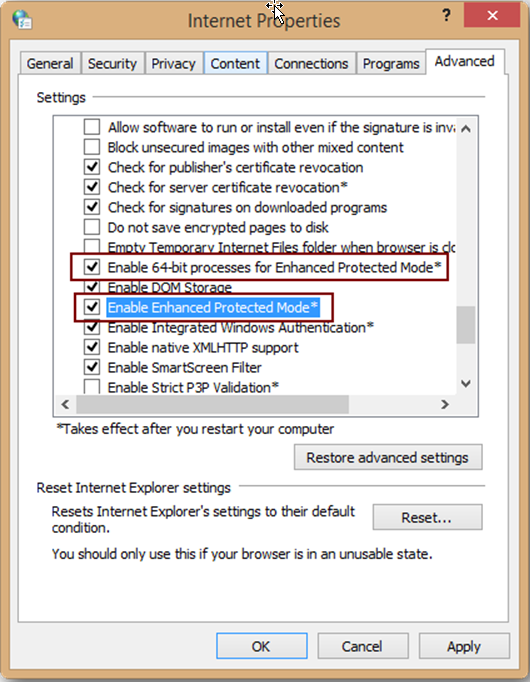
If you’re using a 64-bit version of Windows, you can run Internet Explorer in ‘Enhanced Protected Mode’ and enable 64-bit process mode. If you’re stuck with XP though, there is no way to do this simply because a) x64-bit Windows XP is a rarity, as it’s always been and b) Enhanced Protected Mode is only available for IE10 and IE11. In this case, you can only pray that your antivirus detects the exploitation as it goes on and blocks the payload before execution.
Regular users who rely on Windows for day-to-day tasks should install an alternative browser until the issue gets an official patch from Microsoft. In the case of Windows XP users, they should adopt, if possible, a different third-party browser permanently as they will not get the fix via Automatic Update. If you’re a system administrator maintaining a Windows XP computer network, then you’re probably in for overtime: make sure that you run an antivirus solution with exploit detection features and that you’re disallowing access to the internet from machines running vulnerable versions of the browser.
A final word of advice: this is just the first of a presumably long series of security issues that Windows XP users will encounter in the near future. Windows XP had a good run in its 12-plus years on the market, but now it’s time to say goodbye and move on.
Bogdan Botezatu is senior e-threat analyst at Bitdefender.