What's our online 'star chamber' actually for?
Totalitarian regimes, besides being brutal oppressors of their human subjects, are also often incredibly silly.
At the end of the Ceaușescu regime in cold-war Romania, for instance, one in 44 Romanians was an informant to the secret police, known as the Securitate.
Applied to the Australian population, and assuming there was only one informant per household, that would mean every 15th house in a typical street would have twitching curtains, and be compiling dossiers on who got up to what.
That could never happen in Australia, of course, and nowadays it doesn't need to. These days, the digital trail left by an individual tells security agencies more about what we've been up to than the hundreds of tonnes of paper files kept by the Romanians.
Capturing the digital record will be the job of our major telcos and ISPs if the government's new data-retention bill is passed into law. Naturally, they are moaning about that because it costs them money and doesn't benefit them at all.
Logging internet and IP-based phone records is much cheaper that recruiting all those curtain-twitchers, but that is precisely why the data retention laws now before parliament are more insidious.
To understand why, it's necessary to consider the giant loopholes in the legislation -- more on those in a minute -- but also the relationship between the smart-phone carrying citizen and the agencies given access to that digital trail.
First, the weaknesses. The government is at present willfully glossing over weaknesses in definition in the ‘metadata' that security agencies have asked it to collect.
As Baker and McKenzie partner Patrick Fair told CommsDay this week, the legislation asks an ISP to discard the data relating to what content an internet user asks for. So regular users of, say, nastynaziporn.com are technically still anonymous.
However, it does ask the ISP to record the IP addresses (that is the single number identifying a single user) that landed on that site, and so going back through an ISP's records, those IP addresses can be correlated with users (even where ‘floating IP' addresses are temporarily assigned to users).
That might all sound fine, because as a nation we don't much like ‘nasty nazi porn' or whatever (and yes, I did make that one up). It's easy to see how the security agencies could use this data to break paedophile rings, terrorist groups and so on.
But it's not that simple, for two main reasons.
First, the Coalition has boasted that the number of agencies who can reverse-track internet users (or users of any IP-based communication) in this way would be drastically reduced by the new laws.
Last year, for instance, existing laws allowed for around 320,000 metadata requests to be made of telcos and ISPs, by hundreds of ‘enforcement agencies' -- that term was so loosely defined that minor government agencies and even a few local councils made requests.
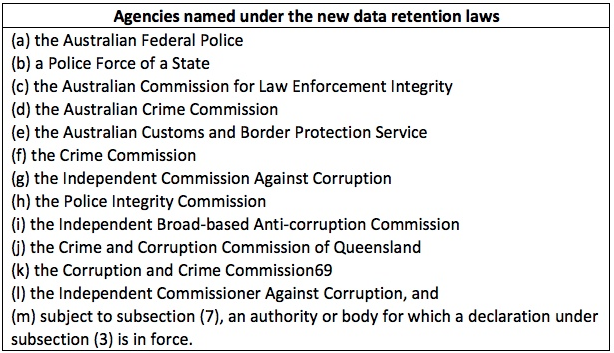
Under the new laws, a dozen agencies -- the real security agencies, not those looking to collect parking fines -- will be defined as ‘criminal law enforcement agencies' who can make these metadata requests (see table below).
However, the list can be added to over time, so other agencies that didn't get a gurnsey -- say the ACCC or ASIC -- might make a case to be declared a ‘criminal law enforcement agency'.
So far, you might wonder, what's the problem? If there are terrorists, paedophiles or the like out there, why not use these laws to catch them?
The answer is chilling. These laws won't catch them, or if they do they will catch the low-level fools who do not know how to use virtual private networks or encryption to remain invisible to this kind of reverse-tracking of internet users. The main perpetrators of those and other vile crimes learned years ago how to do exactly that.
So what are the laws for? The answer to that question is ‘insert paranoid theory here'. My paranoid contribution is that as the US and China compete for geopolitical dominance in our region, it would be very useful to the US in particular to know who's toying with low-level political trouble making here.
Oh, and the Chinese would presumably hack into the same data, so twice the bang for our buck!
Think back to the US interest in Whitlam's turbulent first term, and perhaps that sounds less paranoid -- Troy Bramston detailed some of those fears in The Australian yesterday.
The second reason these laws are far more complicated than the Coalition has tried to argue, is that they are more open to abuse than many realise.
As long as the ‘enemy' is an agreed nasty, such as terrorism, and the good guys are a small, efficient security agency free from corruption, there's no problem.
But to think Australia's security agencies will always be so spotlessly beyond reproach is to forget the lessons of recent history.
It is still only 25 years since Queensland police commissioner Terry Lewis was jailed for corruption, along with several members of the Bjelke-Petersen government, and the ‘special branch' section of Queensland Police was disbanded, accused of a 40-year campaign of intimidation of political activists.
Legislation that will fail to apprehend serious terrorist organisations, or serious criminal gangs, must be viewed suspiciously when the only thing it is capable of is mass surveillance of Australians.
One Canberra policy advisor, who wished not to be named (but who, it should be noted, could soon be identified by such a phone call), argued that security agencies are very good at convincing nervous politicians that expansions of their powers are required.
In this case the politicians are so keen to comply that they cannot fully explain what the laws are for, or what safeguards are in place to ensure that the laws are not just a vehicle for Hollywood studios to pursue copyright theft for movie downloads (which the AFP's Andrew Colvin let slip at a media conference was a real possibility).
Politically, these laws are likely to get more embarrassing over the summer. Though the Bill has been tabled, it is now before a senate committee and therefore cannot pass into law until February next year at the earliest.
In the meantime, there is a rising chorus of opposition from both left and right --when you have the Greens' Scott Ludlam and the IPA's Chris Berg both arguing against these laws, you've got a real political problem.
On the other hand, if the law is passed, and with future mobile phone technologies all set to be IP-based, we'll know exactly when ratbags like Ludlam and Berg have spoken to each other, and with a bit of luck lock them both up for sedition! Oh, what the Ceaușescus would have given for that.
















