Hackers hijacked my iPhone, help!
A post on Apple's support forum
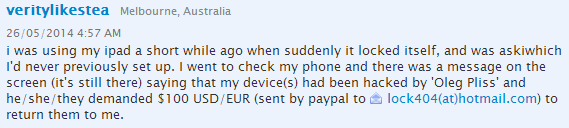
It's designed to protect device owners from thieves, but this week Apple's 'Find My iPhone' feature did exactly the opposite when hackers locked thousands of Australian users out of their devices, demanding a $US100 ransom.
According to IT software vendor Symantec, 'ransomware' attacks like this are on the rise. Just weeks ago, Android mobile phones and tablets were also targeted by ransomware.
So how do hackers get their hands on our personal devices -- and is there anything you can do to prevent it?
What is ransomware?
Ransomware is malicious software -- or malware -- that holds devices or files on them hostage until the victim pays a ransom fee.
The ransomware may take the form of a pop-up message that takes over the device's screen, or it may encrypt files and hand over the encryption key when the ransom is paid.
According to IT security firm McAfee, ransomware was once confined to PCs but the rapid spread of smartphones has seen the problem increasingly occur on mobile devices as well.
The first iPhone ransomware attack was recorded in 2009, but this is the first instance of an attack on non-jailbroken devices.
How were the devices accessed?
McAfee chief technical officer for Europe, Middle East and Asia Raj Simani says the attack doesn't appear to have infected phones with a malicious application. Rather, it exploited Apple's 'Find My iPhone' feature, which allows users to remotely lock their iOS and Mac devices if stolen.
The most likely route for the hackers in this instance is via the victims' Apple iCloud accounts, as all the Australian targets have iCloud accounts.
However, Simani says there has been "no formal confirmation" of this from Apple "so all attempts to determine the cause are merely speculation for now".
Who's behind the attack?
Threat Intelligence founder and chief executive Ty Miller says the attack on Australian Apple device owners bears a striking resemblance to one that occured only last week in the Netherlands.
"A Dutch hacking group going by the name 'Doulci' successfully hacked Apple's iCloud that provided them with the ability to unlock stolen iPhones and then sell them for a profit," Miller says.
"It is quite possible that the same group or a similar technique was used to lock users' devices."
What should I do if I'm targeted?
Miller says victims of the ransomware attack should get in touch with Apple support ASAP, as they can unlock the affected devices.
Users may also be able to get around the problem by restoring to a back-up if they previously had a PIN set, Miller says.
What can I do to prevent this?
If you have an iCloud account, change the password for your Apple ID. However, until Apple identifies and fixes iCloud security weaknesses, says Miller, disabling the Find My iPhone feature in your iCloud settings may be the only way to prevent this particular type of attack from occurring.
It's also worth keeping in mind some other more basic security measures, including:
- Make sure you only download from reputable websites, not third parties
- Be careful where you browse
- Install security software on all your devices
Unfortunately, none of these steps is failsafe. Malware is usually disguised as something more harmless, and in the case of this particular attack, it appears Apple's own iCloud interface -- surely a 'reputable' platform -- has played a role.
Should I be concerned about other devices?
In short, yes. With Apple rumoured to be entering the home automation space, the risks to Apple device devotees could grow exponentially. As the number of devices we use increases, so too does the attack surface for potential malicious actors. And while it's inconvenient to be locked out of your phone or tablet, what if hackers held your home security system to ransom?
A scenario like this is entirely possible through targeted, wireless-based attacks, says Miller.
"Even scarier is through the use of simple 'Google hacking' techniques, where attackers perform advanced Google searches to find unsecured home networks," Miller says.
McAfee's Simani also warns that attacks like these are by no means limited to Apple devices.
"At present many of the well known attacks are proof of concept, but as our reliance on devices grows there is no question that with the Internet of Things, with great opportunity comes great risk," Simani says.
















